Save

How often does a login fail even when someone is trying their best?
We have been spending more time thinking about inclusivity in the parts of a product that people touch most often. Login is one of them. It appears constantly, is usually justified under security requirements, and often causes momentum to break before anything else happens.
In our team, we started noticing how often the loss of momentum came from small details rather than a complete lapse in memory. Someone would feel confident they had the right password, then get blocked anyway. It might be a capital letter in the wrong place, a symbol required on one site but not another, or a password that was updated months ago and never properly stored.
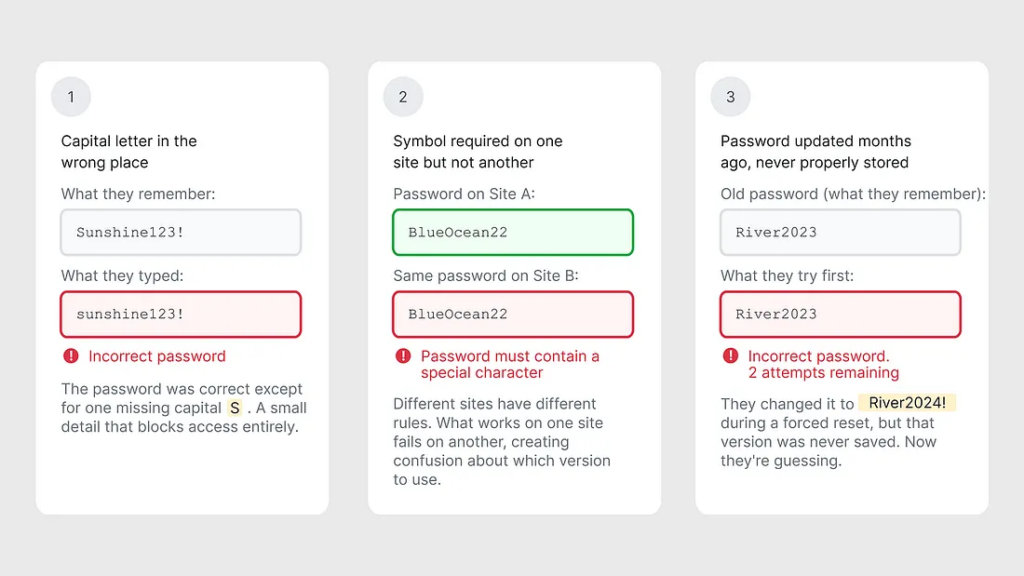
What makes this frustrating is how quickly it escalates. A step that should take seconds turns into a longer sequence of retries, second-guessing, checking notes, and eventually deciding whether to reset. Add the pressure of a warning like “too many attempts,” and it becomes easy to slip into guessing and lockouts.
This friction shows up clearly in metrics. Many companies report login success rates between 60% and 85% under normal conditions, which means a significant portion of legitimate attempts do not succeed. Even when recovery works, it still costs attention and energy, and it often pulls people away from the task they actually came to do.
These failures happen even under relatively favorable circumstances. Logins rarely take place in a quiet, focused setting. They happen between meetings, on a commute, while juggling messages, or at the end of a long day. Glare on a screen, unstable connectivity, or using one hand can be enough to turn a recall-based login into a frustrating experience.
There is also a structural layer that does not always show up in usability testing. Many login systems assume one person controls one email and one password. That is not always how access works.
In Indonesia, email sharing is common in everyday use. Republika has reported examples of people sharing email accounts with friends and family to access apps and services. Accounts can also be set up with help from phone shops or someone at home. When login assumes private, individual credentials, it fails to reflect these realities.
What this means for older adults
For many older adults, this context is common rather than occasional. Memory can be less reliable, eyesight can change, and typing accurately on a small keyboard can take real effort. Research shows that password requirements are often designed with little consideration for age-related cognitive decline, even though remembering passwords becomes harder over time.
When login depends on precise recall, access starts to feel conditional, something that has to be re-earned each time.
Looking closer, the underlying problem is not only age. It is the accumulation of demands. Password login asks people to remember exact details and enter them accurately across many services. Studies have shown that as the number of passwords increases, forgotten and mixed-up passwords increase as well. This phenomenon is why the same login flow can feel manageable one day and unexpectedly difficult the next.
This led us to explore a different starting point.
What if login leaned more on recognition than recall?
Several alternatives to traditional passwords already exist:
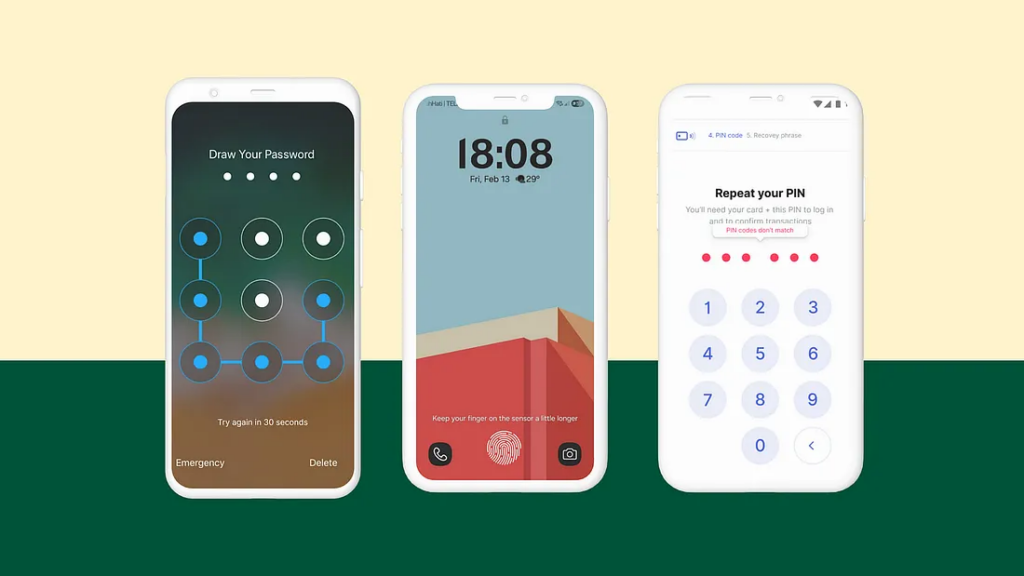
- Pattern locks on Android devices reduce typing burden but share similar problems: simple patterns are straightforward to guess, while complex ones can be as difficult to remember as passwords.
- Biometric authentication using fingerprints or facial recognition can reduce friction significantly, but it requires specific hardware that not everyone has access to, particularly in markets where older or lower-cost phones are common. Biometrics also fail for people with certain disabilities, skin conditions, or injuries, and unlike passwords, you cannot change your fingerprints once compromised.
- PINs are easier to remember than complex passwords, but remain vulnerable when people choose obvious combinations.
Each of these methods emerged to solve real problems. Yet none fully addresses the underlying issue: when conditions are not ideal, whether from missing hardware, physical limitations, or memory constraints, people get locked out.
Password login relies almost entirely on memory. The interface offers very little support when recall fails. Recognition works differently. Rather than generating the correct answer from scratch, individuals select a familiar option from a list. That distinction matters when attention is limited or conditions are less than ideal.
Recognition-based steps reduce dependence on exact typing, case sensitivity, and special-character rules. Errors are less punishing because the interaction is about choosing rather than composing.
From there, we began exploring a recognition-based login where three images are selected during setup and later chosen again from a grid to log in. Research consistently shows that people are better at recognizing images than recalling text strings, and studies involving older adults have found lower rates of forgotten credentials with image-based techniques compared to text-based passwords.

What changes is the mental load during the login moment. With passwords, people have to retrieve an exact string and enter it perfectly, even when attention is divided. With recognition-based login, the interface provides cues. People can select what they recognize rather than reconstructing the password from scratch.
Not a universal solution
Recognition-based login is not appropriate for every context. High-security environments like banking, healthcare systems, or enterprise applications often require multi-factor authentication and stronger verification methods. As one pathway among others, recognition-based login is particularly suited for consumer-facing products where accessibility and reduced friction are priorities, offering a way to reduce avoidable failure for people who are already working harder to complete the same task.
Designing with older adults in mind often reveals where systems rely too heavily on ideal conditions. Login tends to require focus, time, and a steady hand. Real use is messier.
This phenomenon is also the reason why we repeatedly revisited the curb-cut effect. Curb cuts were designed for wheelchair users, but they ended up helping parents with strollers, travelers with luggage, delivery workers, and anyone moving through a city with their hands full. Digital experiences often work the same way. A login path designed for older adults who struggle with recall can also help in everyday situations that teams rarely design around, like glare on a screen, one-handed use, fatigue, or returning after months away. When the front door of a product works for the most constrained moments, it usually works better for everyone.
The article originally appeared on Medium.
Featured image courtesy: Wosunan.
Shannon Joycelyn
Shannon Joycelyn is an experienced product designer at Sixty Two. She crafts thoughtful UX strategies, explores visual ideas, and sweats the UI details because good design should work for everyone.
- The article examines how traditional password-based login systems fail a significant portion of legitimate users, particularly older adults and those in non-Western usage contexts, and argues for recognition-based authentication as a more inclusive alternative, drawing on the curb-cut effect to show that designing for constrained conditions ultimately improves the experience for everyone.